Table of Content
- In this article –
- Why should we protect data?
- Network Security Types –
- Password Disclosure – The root
- Most Frequently Used Passwords of All time
- Some of the techniques that the attackers use –
- Read from the box below to grasp what I mean to convey in the paragraph above –
- Tips to Make Your Network More secure
- # 1 – Reset Passwords
- Use 2-Factor Authorization
- # 2 – Change your network SSID
- Some non-typical but acceptable names for your network –
- # 3 – Turn off network gates when not in use
- Turning off your network system could prove to be advantageous in two ways–
- # 4 – Keep Antivirus Up to date
- # 5 – Monitor Usage Details
- # 6 – Configure Firewall
- # 7 – Hire a security engineer
- ALT TAG – network security engineer salary
- Takeaway
In this article –
-
Network Security explored, and explained.
-
How to setup a secure Network.
Network security is a rather broad term covering technology from multiple dimensions. In layman’s terms, it a set of rules of pre-defined configurations that help computer network know which device is seeking unauthorized access to the data. Every business, regardless of its size, needs to deploy a network security solution to augment the protection overlaying the entire network components.
Today’s network architecture is not as simple as it used to be. Over the past decade a number of developments were made in the field of network security. As the technology protecting data became more and more advanced, so did the threats. With threats as advance as the technology protecting against it, it takes more than just a few lines of codes to protect privacy.
Why should we protect data?
Have a look at the files in your computer that you deem the most precious. It could be an image from your childhood, or an important project you claimed scholarship against. Do you believe you could do with somebody getting hold of this “important data”? Probably No.
Moreover, your device contains sensitive information about you, even your id. One who gets hold of your device gets hold of your identity as well. Who knows, your id could be misused to propagate false political propaganda. Cringed already? Without further ado let’s skip to the crux.
Network Security Types –
The list is unending. However, in this article, we will only make use of the following –
- Antivirus & Antimalware
- Access Control
- Database Requests
- Firewalls
- Segmentation
- Internet Security
- Password Awareness
Read More at : Security-based Services which Every Acute Business should have
Password Disclosure – The root
No matter how advanced the threats may get, password guessing has and will continue to remain the A game for hackers. If I could do an autopsy of all network break-ins that took place last year, you would reckon that in more than half of the cases, the hacker had somehow gained access to the password.
The attacker may brute force into the network. (Brute force involves submitting several passwords simultaneously until the correct guess is made).
Most Frequently Used Passwords of All time
- 123456
- 123456789
- Qwerty
- Password
- 1234567
- 12345678
- 12345
- Iloveyou
- 111111
- 123123
Some of the techniques that the attackers use –
- 60% passwords are phrased from their corresponding usernames.
- More than 50% passwords contain birthdates. Users often modify the numerals in their passwords but only switch back and forth between birth date, month and year.
- “@” is the single most-preferred special character, followed by #.
- “^” is amongst those used the least.
With the above information, I bet if you knew my name you could have easily cracked my password. So, henceforth, stick to the facts I have provided. It is advisable to setup a password which comprises of alphabets, numbers and special characters that convey no meaning whatsoever.
Read from the box below to grasp what I mean to convey in the paragraph above –
User Name – Sophie Walters
Date of birth – 26 January, 1997
Password – Sophie1997
User Name – Gianna Flemings
Date of birth – 24 September, 1996
Password – ah%7ShjOil
For a moment swap places with the person plotting an attack to both the victim’s Instagram account.
Which password would you have guessed more easily, Sophie’s or Gianna’s?
Obviously, Sophie’s.
Tips to Make Your Network More secure
If you have made it this far, let me take a moment to congratulate you. You probably have a good grasp of the basics by now. But before we begin, I should probably pull up a little disclaimer.
Read More at : Network Virtualization: A New Approach to Optimize IT Operations
Disclaimer – though we strongly believe that the following tips will elevate the level of security of your network, it is by no means the route to 100% safe network. No matter how robust the network gets, it is bound to have loopholes. It is only a matter of time that these loopholes are discovered and exploited. We recommend you to continue implementing the standard operating procedures and add our tips to your to-do list.
# 1 – Reset Passwords
Let’s face it. How many of you seriously followed the password protocols we have mentioned above? Not to worry, we did not follow it either until recently.
If you haven’t changed passwords since a long time it is about time you began resetting passwords and security keys. While doing so, make sure to follow the above guidelines or you’d be hitting head against a wall.
Regularly ask your employees to change their passwords as well. Individual computers are the fundamental building blocks of your network, and the façade of your network. Any breach in one of the systems will eventually jeopardize your network anyway, so it is important to secure yourself from all entry points.
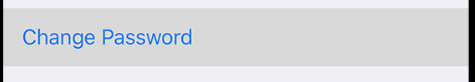
Use 2-Factor Authorization
Some websites have started 2-factor authorization because it almost nullifies unauthorized access to your system. The second phase of authorization prompts you to enter either OTP or a pin mailed to you in real time.
While the probability still remains that the attacker could figure out the OTP generating algorithm, it is just next to none.
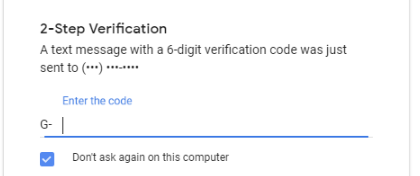
# 2 – Change your network SSID
Unlike how movies portray, hackers no longer work during midnight and wear face masks. Nothing is more evading than normalcy. Hackers, though now more modern than ever, choose to hide in broad daylight.
Hacking, by and large, is not a day’s effort. Depending upon the level of complexity the architecture is built with, a single successful attempt could be an outcome of months of planning and monitoring.
Networks are identified through SSIDs (service set identifier). Each manufacturer has its own vulnerabilities associated with the network so changing names make sense.
The aim is to hide the make and model of your network hardware and regularly changing SSIDs do help. There are no hard-and-fast rules as to how you should name your network. Clearly, that’s one place you are master of your sails but try not to be too provocative.
How not to name your network –
“Hack me if you can”
“Unhackable”
“Important Business Wi-Fi”
These SSIDs are way too lucrative and provocative to not hack. If I resided in your neighborhood, I would not mind taking a few network classes myself to teach you a lesson.
Read More at : Software Defined Data Center – For Best in Class Storage and Networking Virtualization
-
Some non-typical but acceptable names for your network –
“Uncle Joe’s Wi-Fi”
“I am Sober”
“Cannot let you in”
Network names such as these always make for a good laugh. Even if you ran a multi-million business with one of these SSIDs, I would only believe you are a kid residing next door.
# 3 – Turn off network gates when not in use
Unless you are running a global online business, I do not see a need for you to keep your server up at all times. My point is, if your website only operates within a specified region, you should tune your web server to the appropriate timings and shut down network gateways when running idle.
 Though the network security at place is probably robust enough to tackle attacks, why let your website and network sit duck for people with malicious attempts?
Though the network security at place is probably robust enough to tackle attacks, why let your website and network sit duck for people with malicious attempts?
In fewer, simpler words, turn off your network gateways or shut down the entire network if it does not hamper your business operations.
Turning off your network system could prove to be advantageous in two ways–
- It brings down with it, all the malware that may have crept into the network.
- If there was an ongoing breach on your network, the same would shut down in the middle of its operation.
Besides the above two obvious advantages, you will also save precious amounts of data and power.
# 4 – Keep Antivirus Up to date
Antivirus programs release frequent updates with one aim – to safeguard against all the latest threats. Antivirus and other security programs that aren’t updated are good for nothing. While your internet security will still be effective against older threats, the newer malware may go unnoticed and jeopardize the security of your network.
Antivirus should be your last line of defence in a network. If an application has somehow breached into your system, it should not evade your security applications or your network will embark on a journey towards disaster.
# 5 – Monitor Usage Details
How much data do you typically use on your smartphone? Say, 1GB per day. Unless there are applications undergoing major updates the amount of data you use per day would remain more or less the same. Same goes for devices on your network.
Under normal circumstances any device on the network should use the same amount of data and system resources that it normally does. Any hike or drop in usage alludes to the system deviating from its usual – one thing that should raise suspicion immediately.
Before you begin, however, you need data from the past to stack with that in real-time. How would you otherwise know what’s normal for the system without having previous data to compare with.
Below, I have attached a screenshot of my network with all the connected devices listed.
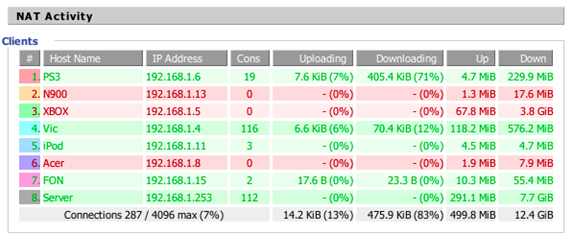
Now, I know how much data my iPod and PS3 eat up together, though here I had them both on standby. The Vic appeared to be using a tad bit data more (it normally use only 2-3% of uploading and downloading bandwidths).
Note that I had deliberately put Vic on update so that I could show you the impact it would have on my network.
# 6 – Configure Firewall
Firewalls aren’t just software applications running on your computer, they come as hardware as well.
A Firewall as hardware does pretty much the same work as its software variant except that it adds another layer of security to the network.

The best thing about firewalls (hardware) is that they do not eat resource from your system and perform better than its software counterpart. If your network did not come pre-configured with a firewall, we strongly recommend you get one. Or, if the budget is being a roadblock, you can deploy the software variant of the same.
Read More at : Key Aspects of Web Application Firewalls that Should Never be Ignored
# 7 – Hire a security engineer
For an absolute beginner, network security can have significant learning curves, one that would take months (or years) to master.
A shorter course is to hire a security engineer, but, let me remind you, it won’t come cheap, given there aren’t many security engineers in the market. Still, the expertise that would come along with him is worth all the money he asks.
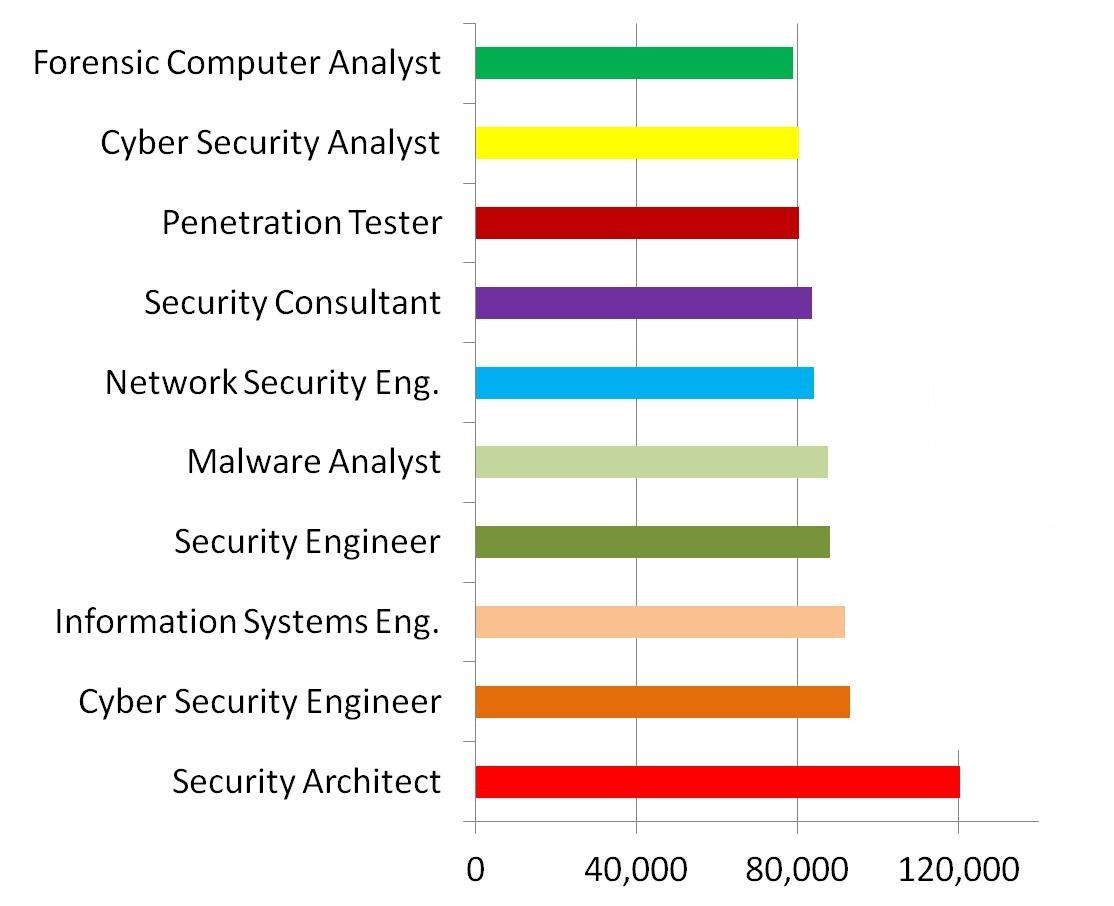 Image Source – Degreequery.com
Image Source – Degreequery.com
ALT TAG – network security engineer salary
Moreover, you have more to lose than gain if you do not hire an expert. If your network gets jeopardized even once, sensitive data can end up in wrong hands. If this happens, not only would your brand lose its reputation but also all channel of sales that you had long relied upon.
Takeaway
With ongoing coronavirus pandemic and increased reliance on the internet resulting from it, we need network security more than ever. Securing network should be the top priority for every business. The aforesaid tips can prove to be useful even for people who are not very well-versed with networks. With the tricks shared, we hope you now know how to setup a secure network. Not to forget, network management requires years of experience and a few more years of implementation to master completely.
We have been receiving queries for securing Wi-Fi network and to be precise enterprise networks and Wi-Fi’s aren’t very different. You can secure your Wi-Fi the same way you secure every other network. The thing with wireless networks such as Wi-Fi is that there is not much to lose. Enterprise networks, if not secured, can lead to a catastrophe though.
Read More at : How To Secure Your Data For Transport In Cloud?






 Live Chat
Live Chat