As innovations are reforming the business economy, CIOs have become more serious and cognitive when planning to integrate a technology solution. Right from the CEOs to company executives, all have zero tolerance for data loss and downtime issues. Over and over again, such organizations set a priority for their critical applications and data, which is accessed on a day-to-day basis. However, there are still many left who have not stumbled upon to the right solution that can keep up with these escalating expectations of maintaining flawless business availability.
In fact, according to a survey, more than 75% of chief technology officers confess that they find teething troubles for maintaining round the clock IT service availability. It goes without saying that aging legacy systems and data protection techniques have become obsolete in combatting the harsh realities of the threat-affected IT world. The emergence of cloud computing, virtualization, BYOD, and stress on the Internet-connected world have made customary methodology a fiddly, frustrating affair. Seemingly an advanced tech-inclusive approach to enterprise applications has been proven to radically boost productivity.
This blog attempts to describe how data protection and performance-driven availability solutions can help you overcome potential shortcomings:
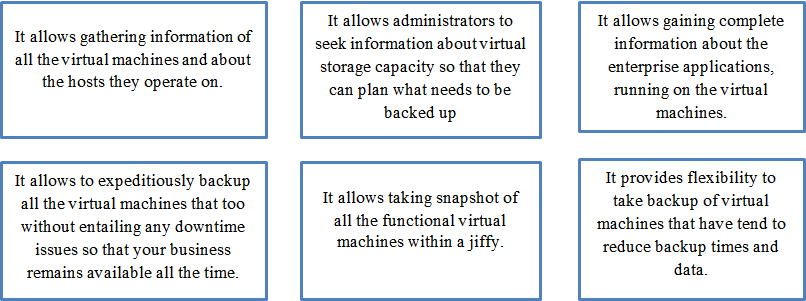
With continual growth of data plaguing many organizations, it is up to the reliable solutions to help overcome the availability and security chaos. However, with a diverse portfolio of choices permeating the market, how do you choose the best one? A host of protection tools are available today, amid them only a few of them are virtualization-centric. Not to mention, conventional legacy systems treat all server variants same as the physical servers, this might act as Achilles heel for your business. Every server encompasses different set of configurations and operating systems, thus, possibilities of technical disputes are greater especially when you are endeavoring to backup or recover your mission-critical files. Let’s say, extensive file-based backups are only taken when small blocks of data have got modified. Here is the catch; business availability solutions designed bearing virtualization in mind establishes a smooth link with virtualized architecture, which unlocks many benefits with a single key, such as:
This is not where the world of advantages ends! You won’t expect what else benefits you can withdraw by embracing virtualization based availability tools as compared to other legacy systems. Just to add, this smooth connection helps in taking automated backup of selected applications and allows recovering failed VMs within minutes. In addition to this, it also lets users to gain quick access to their organization-essential applications so that business functions do not come to a halt owing to data inaccessibility or Virtual Machine failure tremors. In addition to this, administrators need not to worry about complex process of backing up the data or securing it against vulnerable attacks as it is fully automated.
Fall-out Reasons
Surplus legacy data protection tools have come into existence proclaiming to play a herculean task for ascertaining unmatched data protection and accessibility. However, the facade turned different as many of them failed to fulfill the requisite purpose, and the reason representing there failure was they weren’t built keeping virtualization in mind. As virtualization is expected to complete transform the way organizations process their operations, it is wise to integrate a business availability solution that is best-suited for virtualized environment, and enables fastest recovery, uninterrupted accessibility, zero data loss, and stringent protection against all nuisances.
Maintaining and managing a data center facility is an intricate practice as a host of key metrics such as data points, security systems, professionals, and other IT components play a pivotal role in determining the fitness of a data center. IT managers are in a constant pressure of delivering more in a limited budget assigned by the CFOs, which is why they often take some of the core data center errands including availability for granted. Moreover, most of them stay reluctant to upgrade their legacy backup and protection systems and strive to meet the business demands with these outdated systems. This, in turn, leads to downtime, data loss and gives birth to other potential shortcomings. Another reason cited by experts for data center failure is stagnancy of CFOs in allocating fund for innovative technologies, which evidently curtails business growth.
The Success Mantra is Right Here:
It goes without saying that top performing organizations stick to the data center hosts that employ solutions that meets robust functionality and addresses security issues, offer quick data insight, all without negotiating with always-on, always-available business mantra. A successful data center in India facility signifies 24/7 uninterrupted business operations, reduces downtime and data loss, and supports ever-increasing amounts of data. It is indispensable to define the appropriate availability requirement for your business. According to study, data loss can cost businesses around $3 million in just one year, and downtime can cost around $9-20 million in one year. Herein, automated availability solutions that encompass a layered pattern (practice different approaches to backup applications on as many as possible mediums, such as VM replication, local disk backup, and storage based snapshots) and support distinct virtualized platforms can be of a great help.






 Live Chat
Live Chat