As companies are battling with rising cybercrime rate, it has become imperative for them to turn into a more distributed model and add additional security endpoints throughout their network. Any vulnerability or safety deficiency can adversely impact their confidential data as well as IT infrastructure.
Considering this scenario where the endpoint security of an organization is at an extremely critical juncture, many companies have migrated their network to the cloud. In this light, it is worth understanding how cloud computing is acting as a new way of protecting enterprise assets, without distressing its cost structure and other management overheads like scalability, agility, and performance. Here’s how!
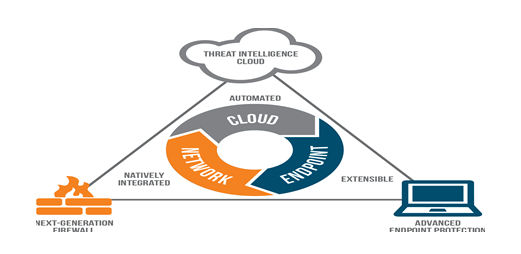
Let’s begin with the concept itself. So what exactly is endpoint security? It primarily refers to an approach followed by an enterprise to protect its corporate network while accessing it through remote devices like mobile phones, laptops, and any other wireless device. Every single device remotely connected to the company’s network act as a possible entry point for safety threats. For this reason, even the most established corporations follow a secured approach to ensure their network safety.
Besides, the recent columns of many magazines and newspapers have demonstrated the cost and scope of data breaches in an organization can be exceptionally high. As a result, many IT professionals are on a lookout for key survival hangs to ascertain and balance-off such risks.
And so, perhaps the next question is how cloud computing as an alternate solution can get the ball rolling? If we go by the latest report elucidated by the Harvard Business Review, approximately 84% organizations have expanded their Cloud utilization. This major migration to the computing platform is fuelled by higher cost savings, greater scalability, better visibility, and seamless integration with the Cloud architecture.
With this kind of entrepreneurial IT makeover, it makes sense to protect a corporation’s security endpoints by making a move to the cloud. Likewise, other critical; factors that have compelled users to integrate their deployment and distribution ecosystem to the secured cloud architecture are listed as below:
Flips Benefit from Attackers to Security Defenders: In the current scenario, attackers are equipped with the most creative and thriving techniques to gain access to an organization’s confidential information and earn money through cybercrime. They make use of conventional security software system, network packages, or any other solution to figure out ways that tick. In this regard, cloud computing recreates a mock network for endpoint protection systems to bypass attacker’s technology. In addition, these adversaries are capable of running numerous lab mock attacks to create real time information on potential attacks. Essentially, in this scenario, when every technology can break down, cloud model has worked reasonably well. It is further observed that with cloud-enabled security model, adversaries may possibly access the endpoint sensors yet protect victims against every singular attack. Besides, the cloud model further records, analyses, and shares such attacks to prevent its subsequent occurrence.
Real-Time Behavioral Analysis: Another important feature of cloud architecture is its ability to register and study attacks and accordingly perform crowdsourcing intelligence to pick up attack techniques throughout the network in a real time. This means, the more data and information captured in the Cloud security model, the better insights it yields. In traditional on premise security model, it is argued that the models can only detect attack and make them initially unsuccessful. However, eventually an attacker determines the point where attack was previously detected and accordingly adapts to these approaches to dodge the detection and employ undetected methods to gain access to that point. On the other hand, Cloud architecture makes use of real-time interactive study and response at each and every stage of the cyber-attack, and not only at the detection point. This entails favourable advantage to the defender.
Protects Sensitive & Confidential Information Without a Miss: The Cloud endpoint security model stores and transmits merely meta data in order to avert the delivery of potentially sensitive and confidential information located at the endpoint. Furthermore, the service providers offering cloud solutions follow highest security standards to ensure the privacy, confidentiality, and integrity of the enterprise information. For this reason, these web server providers are able to effectively detect and address any security concerns and appropriately isolate information that may affect customer’s privacy.
Round-the-Clock Network Protection: With the introduction of BYOD movable workforce concept, employees are frequently opting to work from multiple locations. In this purview, the endpoint security software employed via VPN must be accurately installed and connected to devices to safely support everyday activity of the workforce. Cloud endpoint security model, on the contrary, makes it feasible to remotely manage company’s assets on the network and hence boots out a company from maintaining and managing protection console for its overflowing database. The Cloud model works on/off the network.
Simplicity & Scalability of the Cloud-based Platform: A practical reason that replaced an organization’s on premise solution with the Cloud architecture is attributed largely to the scalability and simplicity of managing this computing model. It is further established that the model has capability of safeguarding an enterprise assets on/off the organizational network. In contrast, the traditional on-premises security endpoint models require regular upgradation from the vendor, which at times, can prove painful for the corporation. This further strengthens the reason why companies need to migrate to the cloud.
Above and all, it is possible with the cloud hosting architecture to maintain and store aggregated information, without any problem. The model keeps the information centralized in an encrypted format to ensure access to the right people only. It can be dynamically scaled to only pay for the indispensable resources, without costing a great deal to the organization. Adding more, right security measures only help to cut the mustard.






 Live Chat
Live Chat