Table of Content
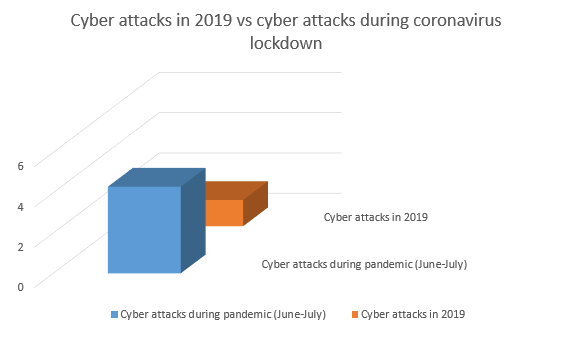
The world might be fighting the ‘never seen before’ coronavirus pandemic, but IT has its own problems to deal with. With a plethora of employees working from home, the level of security has taken an obvious dig. The result is an unusual increase in cyberattacks. Our survey indicates that in just two months there have been more attacks than there had been in all of 2019.
Cyber attackers are eyeing business professionals working from home
Hackers had never been more active. But what is the key reason that has attackers eyeing on the added opportunities? Here’s our opinion on the matter.
Before the coronavirus lockdown, most people worked from the office. While working from office might sound like primitive now, it was a safer and better way from a security perspective.
Organizations deploy plenty of security parameters – hardware and security applications – to safeguard their network.
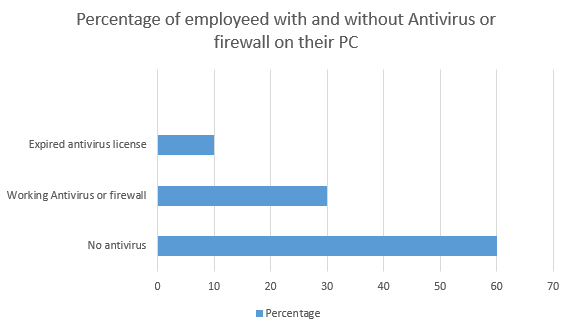
More than 60% of users in our organization did not have antivirus or firewall installed on their personal laptops/computers. A substantial 10% had security applications but the licence stood expired.
Recommend Read : Considerations for choosing a suitable Web Application Firewall
When work from home was permitted, organizations allowed public access to their network to make it accessible to employees working from home. Since the workstation from which they were accessing this network was vulnerable, cyber attackers had little troubles breaking in.
How to protect your network? In a nutshell
There are several ways to protect your network, we will specifically narrow down our discussion to firewalls. If you have great firewall security at the place, you can do away with other less-relevant security apps, although we don’t recommend doing that either.
Firewalls are the most effective against phishing attacks through which hackers lure users into a spoof website and convince them to enter confidential details such as credit card details, or bank ID.
The hackers may also guise themselves to look like a legitimate business and ask you to download the app or click a link. Right when you do so, a clandestine code is downloaded on your local system, which regularly sends information to the owner.
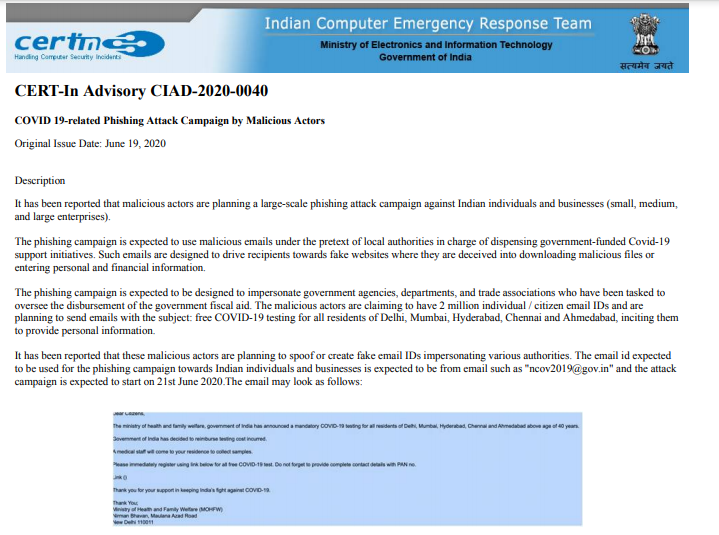
Through phishing, hackers lure the user to click on a link and download the malicious code on their system. Through this opening, they can steal confidential information and direct more attacks on the network.
Recommended Read : Multi-faceted Advantages of Web Application Firewalls
There isn’t a better time to install firewall
There has never been a better time to configure the firewall on your system and the system of your clients. At Go4hosting, we regularly do that. Our systems are so programmed that we know which of our clients has no firewall system at the place and our next step is to install a firewall.
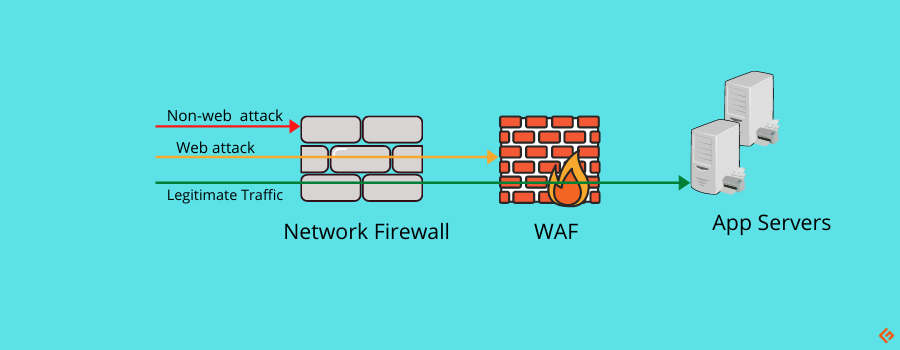
Firewalls systems act as a barrier to malicious traffic, only allowing the legitimate visitors access to your system. So let us go ahead without further ado.
How to choose a Firewall
Installing Firewall isn’t a difficult thing to do and you’d more or less master it in one go. But before you choose one, you need to consider the following –
- Configure firewall
- Secure access to the firewall
- Define a network and its architecture
- Test the firewall before go-live
Before you can configure firewall, you need help choosing the right one for your business. The selection process can be tricky and the choice varies depending upon the organization size and its infrastructure.
Irrespective of how big (or small) your organization is, the firewall must have the following –
- Web or Traffic filtering
The firewall must have the capability of blocking unwanted traffic the entry to the network. Put simply, it should be robust enough to filter out unwanted and malicious traffic from genuine, legitimate visitors.
Although automatic, the Firewall system relies on you to create your own rules. Thus, it is your job, as an administrator, to define rules that allow and restrict access to the content on your website.
- Virtual Private Networks (VPNs)
VPNs or Virtual private networks are a must-have. If your Firewall doesn’t have one, it is up to no good. A virtual private network allows you to have your own private network. You can be selective of the people allowed to connect through the VPN.
Read our guide on how to connect to a work PC using VPN.
One of the first things that Go4hosting did during the pandemic was establishing a VPN and directing employees to install an application through which our internal network could be installed. We were, at all times, wary of the number of users connected and kept an eye 24/7 so no one else other than our own people could connect.
When connected through VPN, hackers can neither extract data nor track the internet activity of a user because VPN hides online footprints.
- Malware and virus blocking
Most firewalls are robust enough to also filter out malware and viruses from your system. Almost all the dedicated servers on our data centers have firewalls that undertake this functionality.
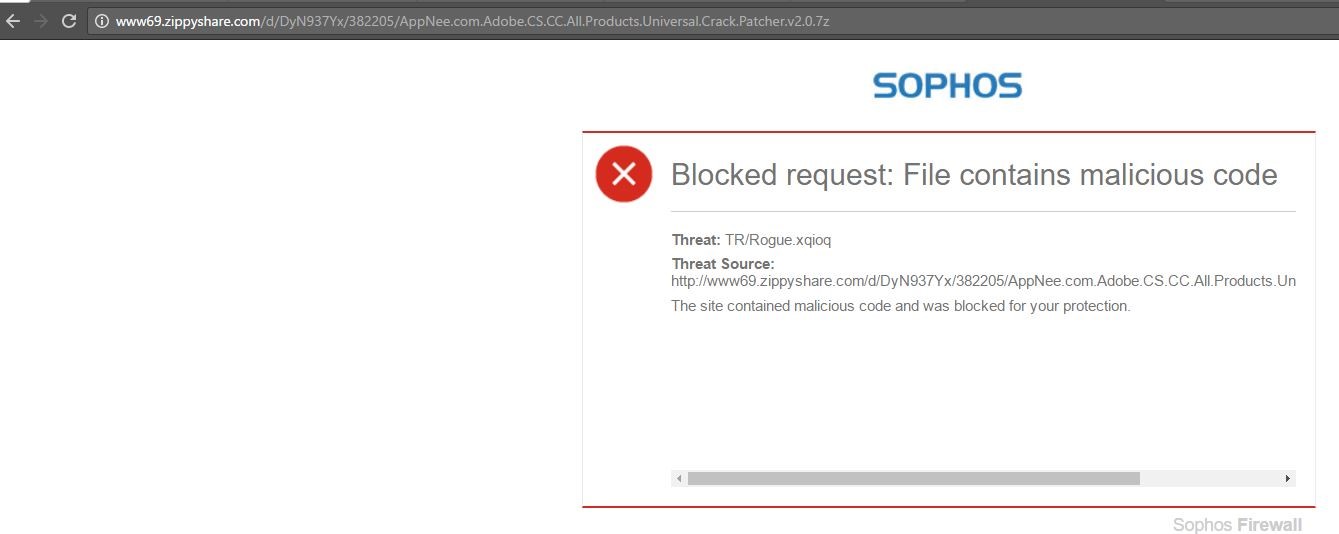
If at any point, the system is invaded by a virus, the firewall will simultaneously disconnect the system from the network and move the threat to the chest before it does any damage to your system.
- Intrusion prevention system (IPS)
Intrusion prevention system is more of a necessity for data center operators like us.
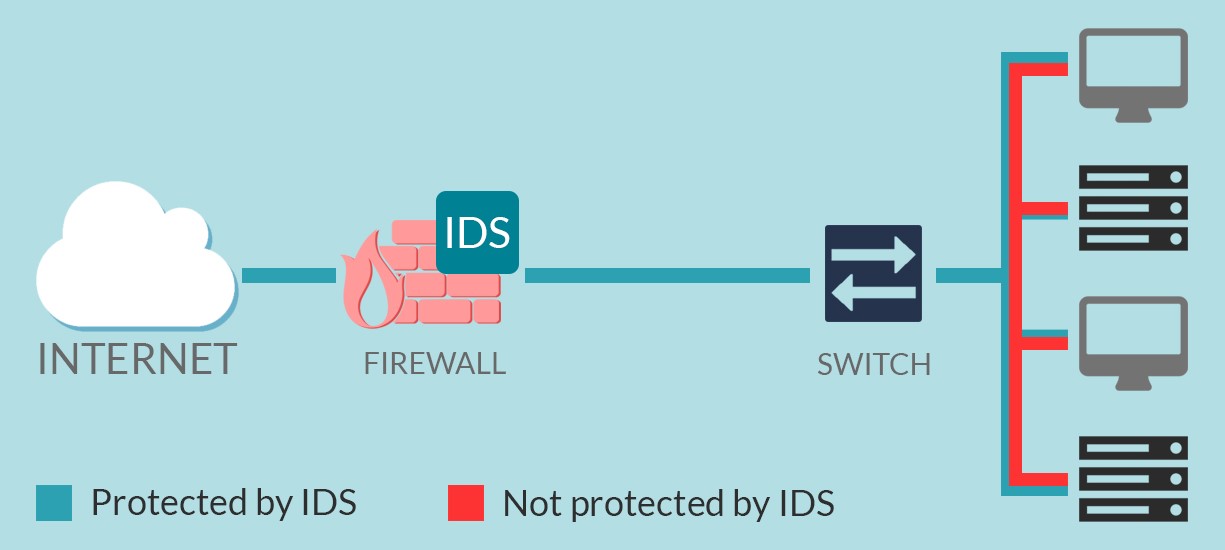
IDS – Intrusion detection system
IPS constantly monitors the network and alerts its administrators during an unwanted intrusion. The administrators can then take suitable actions to secure that system.
- Deep packet inspection
There aren’t many firewall applications that can perform deep packet inspection (DPI). DPI is a feature wherein the firewall inspects data packets passing through the network. Based on pre-defined rules, the firewall may then either allow data packet to pass or block it then and there.
Coming on to the most pressing question – how to install a firewall on your server?
Installing firewall primarily consists of the following four steps –
Step 1: Decide who can access the firewall and who cannot
Ideally, you shouldn’t allow anyone but a few people the access to your company’s firewall. The more people you share login credentials with, the more likely it is that your systems will be misused.
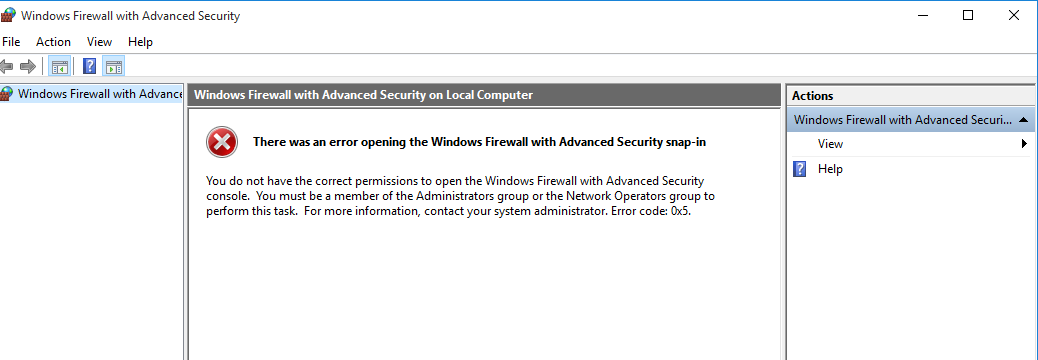
(Our administrator has denied access to even Windows firewall on our computer. You should adopt similar practice on your network too).
Hence, the best thing to do is to only allow select people the administrator access. So, the best thing to do is to create users with limited privileges and then secure logins with strong, random passwords.
Step 2: Define the architecture of your network
Having set up the access controls, you should create several layers of data on your network. Doing so will help you to dig the data layer by layer. You can then define separate rules on separate data layers. This gives you more freedom over your firewall while also securing your network infra.
More the layers of data, more secure the network becomes.
This, though beneficial, comes at the cost of increased complexity of resources.
Step 3: Configure firewall settings
Here comes the most crucial step, where you need to configure and set rules to control both incoming and outgoing traffic on your dedicated server.
(The transfer protocols that you should allow and disallow on your server)
Following are the options that you will likely find while defining rules on your server –
- Allow all– this setting will enable all types of activities on your server.
- Deny all– this setting will restrict any type of traffic from entering your server.
- Customize or define rules– perhaps the most and only setting enabled by network administrators. It allows user to customize and make their own rules on what type of traffic they want to allow and disallow on their server.
Step 4: Testing
No matter how convincing the settings look, never make your firewall go live until you have tested it.
Validate whether the rules that you have defined are working. If the firewall is indeed blocking traffic, verify that it is blocking the right traffic and not legitimate visitors.
Always have a firewall on your client’s dedicated servers
Firewall comes in both hardware and application variants. Which one should you choose? We recommend deploying both. You can never have enough of security because there would always be underlying loopholes.
Installing a quality network firewall would secure your system.






 Live Chat
Live Chat