Before getting into DNS invasion, let’s understand the bigger picture i.e DNS security and why it is important?
DNS Security and Why It is Important?
DNS (Domain Name System) helps in converting human-readable domain names into IP-addresses. IP addresses are very complex and hence cannot be remembered or perceived by average human brains. But domain names are very easily readable and remembered. (For EG. Trademark.com). let’s understand the difference between Domain name and IP address.
| Domain Name | IP Address |
| Domain names are of variable length | IP address is of fixed length (4 parts) |
| Easy to read and remember | Difficult to remember the integers |
| Domain names carries no information to help route packets towards them | Routing information embedded without them |
Now when you have understood the concept of Domain name system, it would be easy for you to understand DNSSEC (Domain Name System Security Extension).

DNSSEC is a technology that was developed to protect information that is carried by the DNS that is used on IP networks. It authenticates the origin of the DNS data, forward lookup zones and thus acts as a defense mechanism against all the attacks. This technology preserves and protects that overall data integrity.
Working of DNSSEC
is DNS was built similar to a phone directory but apart from telling your system to where to send it also receives information from multiple addresses. This random acceptance of addresses creates a loophole in the DNS security and a passage inside any IT infrastructure. Not only addresses, but email servers also use DNS to route the messages that make them also vulnerable enough towards security issues in the infrastructure. Thus, DNSSEC is the security protocol for all those medium wherein DNS is used by adding up a layer of trust on top of DNS.
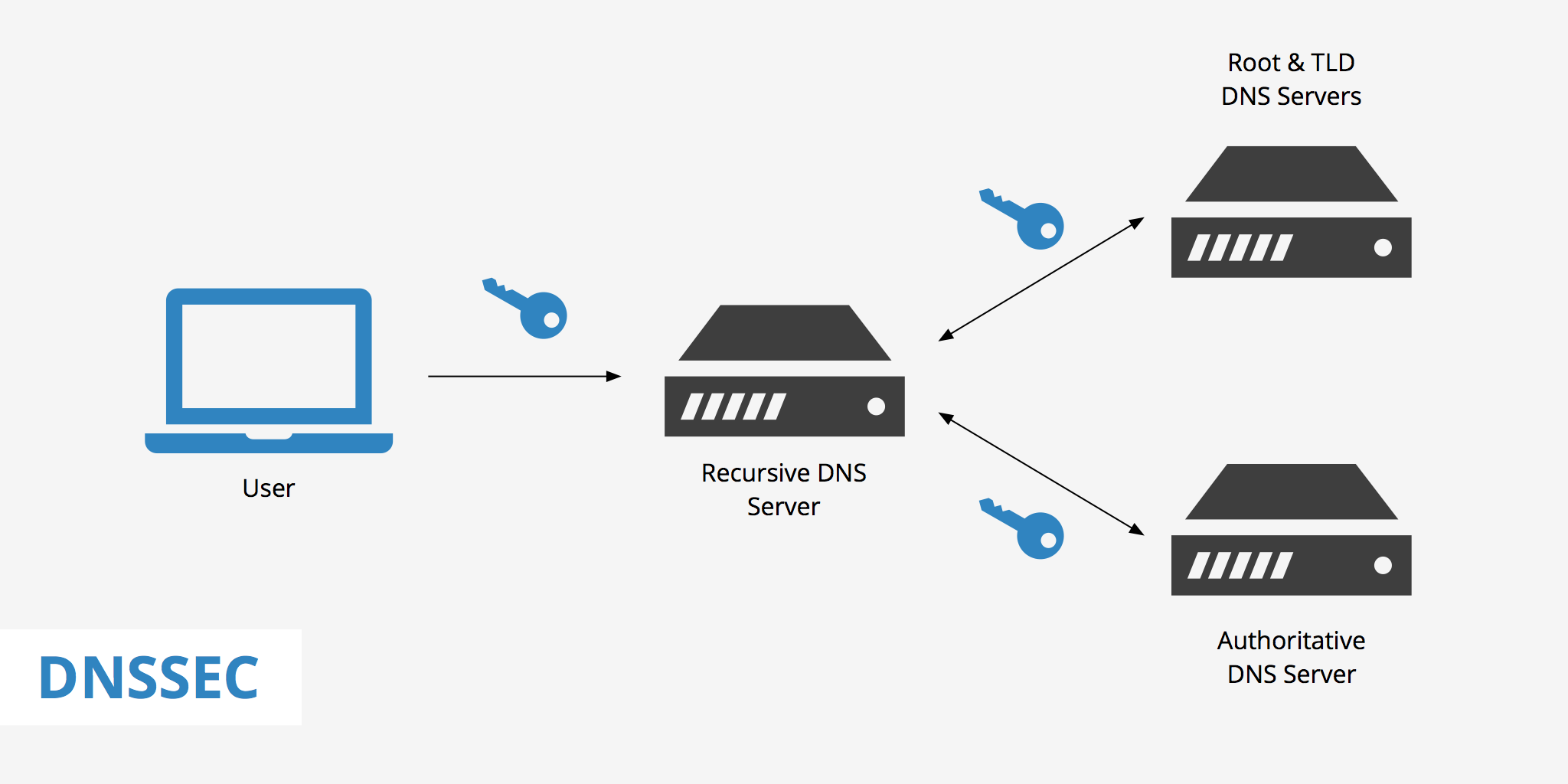
See DNSSEC Conceals the Domain Name and the End User is Directed to the Authentic Domain Name
DNSSEC prevents the attackers from hijacking a DNS lookup to fulfill any of their malicious purposes or forgery by a signing process by assigning unique signatures that cannot be hackneyed in fact not even once. Any concerned person with the right set of expertise can identify the signature and verify it whether it coming from an authenticated address or not. These signatures are more than enough to ensure that data has tampered or not. The steps it follows across all the layers of the DNS are-
Root DNS server signs the key for the .COM NAMESERVER <—–>.COM NAMESERVER then signs a key for the Google.com’s Authoritative Name server
DNSSEC uses some extensions to reinforce security like ensuring the recipient of the data to verify the source, authenticated denial of existence to check whether a domain name exists or not and confirming data integrity to check if there is any alteration in the data while it was in transit. Using Reverse Lookup Zones also caters to a sense of authority to the DNS forwarding zone and helps in resolving IP addresses to network resource names.
DNS Attacks and Its Types
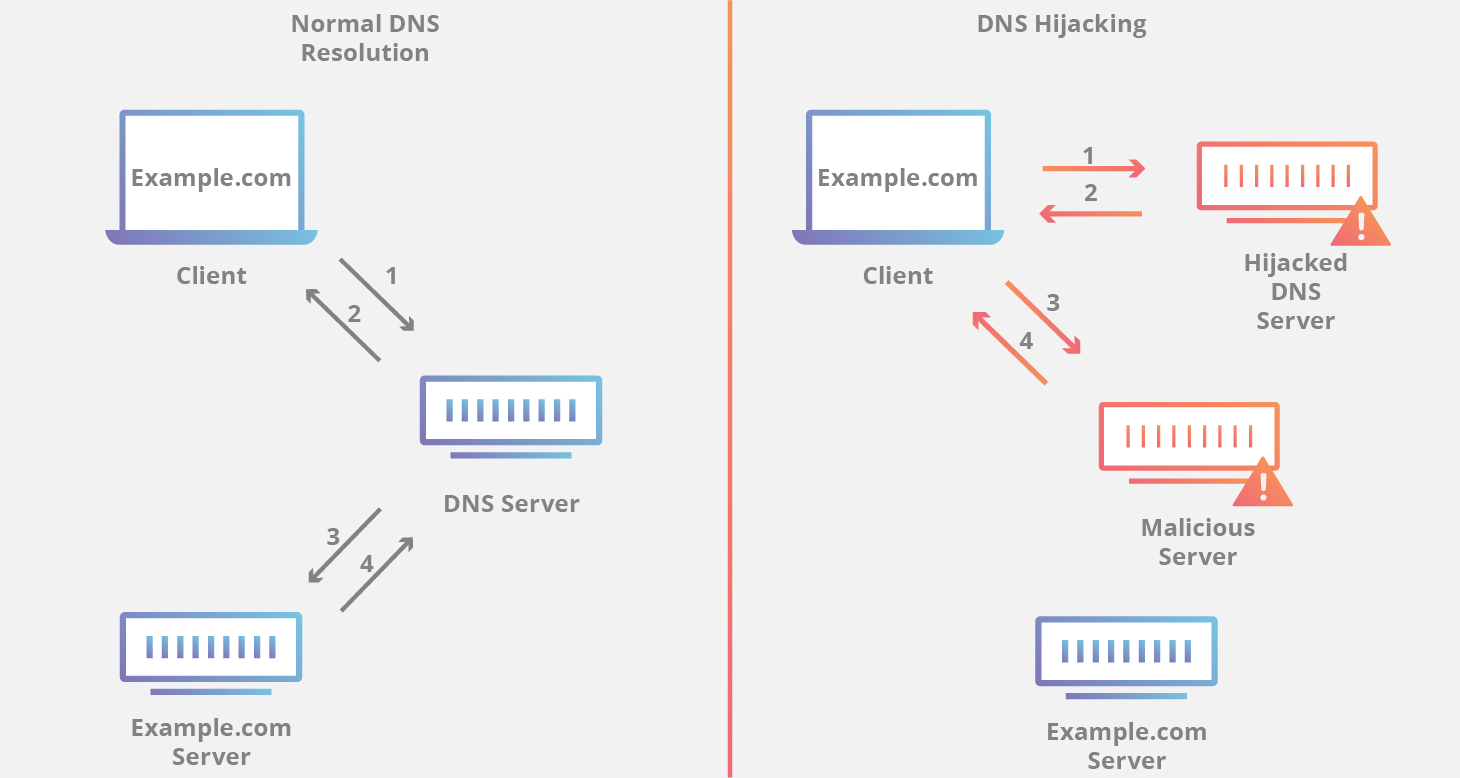 See How the Domain Name has been Played Here to Deceive the End User by Showing the Similar Domain Name
See How the Domain Name has been Played Here to Deceive the End User by Showing the Similar Domain Name
The traditional DNS infrastructure was prone to more attacks, so it was in an immediate need of a hardened DNS layer to minimize the risks. Network security developers and engineers worked day and night to develop a method to identify the symptoms and generating a more responsive action. DNS attacks are performed with varying sets of intentions. It can be conducted for financial, political gain, hacking satisfaction, etc. But irrespective of the intention every DNS attack is devastating for any organization. To understand it more deeply let us go through the features of DNS that attracts more and more hackers-
- Complexity– The complex management of DNS makes room for inevitable mistakes. This has been creating possibilities for occasional mis-configurations or some kind of operational mistake. To make domain names unique from others, administrators all around the world started playing with the external names. These syntax errors helped them to keep the data accessed by only a specific set of people who are aware of that modification in the name.
- Vulnerability– This one of the architectural challenges that is counted to be one of the major security flaws in the design. The vulnerability of the DNS design needs some simple counteractive actions to process these recursive queries. But better results can be obtained if these design implications are fixed on time and will then prevent the name to be open for recursive queries. The vulnerability arising from arbitrary IP addresses leads to cache poisoning. For EG. A potential hacker can create the replica of a banking site by keeping the exact same content and level of authenticity and then can steal thousands of bank accounts and passwords.
- Challenging Upgradation- Upgrading to new software will demand downloading of a new source code, compiling, testing and installing it. Then when once the downloading procedures are completed, there will be compatibility issues. The new version will not be compatible with the previous zone data or documentation. This gradually becomes a big problem fir the administrators and if not brought under control in time then it becomes even worse.
Types of DNS Attacks
With growing times in the IT sphere, hackers have also come up with advanced hacking techniques. Talking about the hackers, mentioning different types of DNS attacks will make it more clear about the level of DNS lookup invasion. These are the types of DNS attacks –
|
|
Volumetric Attacks |
Protocol Attacks |
Application Attacks |
|
Description |
Attacks that use massive amount of traffic saturating the bandwidth of the target. Volumetric attacks are easy to generate by employing simple amplification techniques |
Attacks that render a target in-accessible by exploiting a weakness in the Layer 3 and Layer 4 protocol stack |
Attacks that exploit a weakness in the Layer 7 protocol stack. It is the most sophisticated of all the attacks but most challenging to identify and ease at the same time |
|
Level of attack |
The sheer quantity of traffic generated by the attack can completely block access to the end-resource. The magnitude of the attack is commonly measured in bits or packets per second |
Protocol attacks consume all the processing capacity of the attacked target or intermediate critical resources like a firewall causing service disruption. |
Application attacks establish a connection with the target and then exhaust the server resources by monopolizing processes and transactions |
|
Examples |
NTP Amplification, DNS Amplification, UDP Flood, TCP Flood |
Sync Flood, Ping of Death |
HTTP Flood, Attack on DNS Services |
DNS Spoofing
Apart from these general DNS attacks, DNS is also prone to spoofing activities. It is a type of attack wherein the user is navigated to a fake website that looks like a real one. This you as a user might have also experienced many times in your daily work. The traffic is diverted to a legal looking yet so illegal website and thus inviting multiple thefts. Even a single click or tap can capture your crucial credentials and you will only get to know about the theft once you have already been coned or in the procedure of it. Sometimes this spoofing can be prolonged and you won’t get a single hint about any act.
How to Get Away with DNS Attacks?
After getting to know about the severity of DNS attacks, you might be feeling that it would be tough to get away with such kinds of attacks. But if steps are taken in the right direction and at the right time these attacks can be avoided very easily. These steps are really important and especially for those website owners who have to deal with user’s sensitive details like bank account credentials etc. These precautionary steps will turn out to be magical for them-
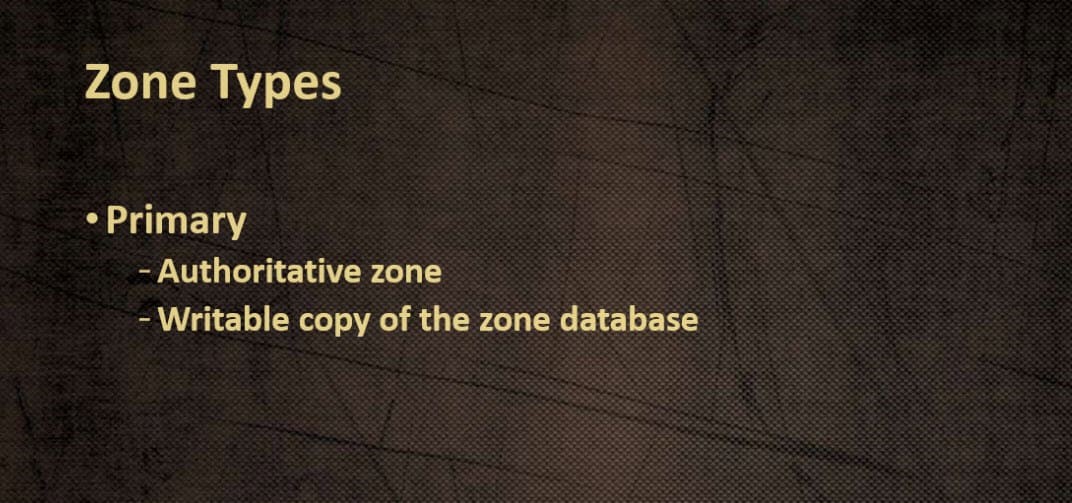
- Constant Auditing of DNS Zones–
Before looking for any other method, reviewing your DNS zone will come out to be most beneficial. Once much time passes after your website has gone live, some sub-domains have been inactive for a long time. These domains gradually become hot spots or say the most vulnerable points for the attackers. Hence, going through all the DNS public records at regular time intervals, reviewing all the zones be it forward lookup zone, reverse lookup zone or DNS forwarding zone.

- Updating DNS Server–
Keeping the DNS server up to date saves you from attracting further more attackers. For this if your website is hosted with a hosting provider then select the one that has the capacity and resources to test and try things. With Go4hosting you will not have to worry about, our hosting packages are already configured with the same.
- Hide Version Numbers-
Most of the attackers try to attack by trying out different version number queries and just wait for the one to match with the real one. The DNS server must hide the version numbers that would reduce the probability for the attackers to match the one with yours.
- Limitation on Zone Transfer-
Copying of the DNS zone for transferring is used by many of the servers. Attackers love to perform DNS zone transferring to get a deeper look into your security infrastructure. To prevent this, restricting the IP addresses for zone transfer would be the first and foremost solution.
- Deactivating DNS Recursion-
DNS poisoning can be prevented by disabling DNS recursion. But what does DNS recursion allows on your DNS server?
DNS recursion allows recursive queries to run on the domain of your server. By restricting this third party hosts will not be able to search queries for name servers.
- Isolating DNS Servers-
Running your own server or going for dedicated hosting will save your DNS server from many of the attacks as it will get that dedicated care. All the DNS services will be operating for your single server. Go4hosting dedicated server hosting will help you in achieving this and will protect your DNS server like their own.
Thus DNS invasion is too much in the trend and before you become a victim of the same, you must take steps that are needed to protect your DNS server. Actions taken in time can save a lot of money and pain that comes with any of the cyber-attacks.






 Live Chat
Live Chat