Table of Content
- Ransomware Meaning
- Is Ransomware a Virus or a Malware?
- How Ransomware Works
- Ransom Attacks by WannaCry
- What was the WannaCry ransomware attack?
- What harm can a ransomware do to my computer?
- Guise is the key
- Who is likely to be a target of ransomware?
- Ransomware attacks in India have surged since coronavirus outbreak
- The International Picture of Ransomware
- Ransomware Extension List
- What to do to avoid ransomware
- Ransomware Can Spread Very Quickly – The Main Problem
- How to decrypt files encrypted by ransomware
- Ransomware decrypt tools that are worth the try
- Takeaway –
Ransomware Meaning
Ransomware is a malware type that has the capability to encrypt files on the victim’s computers. The attacker, after launching ransomware attacks, demands payoff to decrypt files and restore access to the computer.
Each ransom also displays instructions to the user on how to proceed with the payment. Ransoms vary from a few hundred dollars to a few thousands, even millions in some cases. Attackers ask you to pay through anonymous channels, mainly Bitcoins.
Victims are provided with the encryption key only after the ransom has been confirmed as received by the attacker. There is no surety that the attacker would unlock the computer even after you have paid.
In this blog you will learn –
- What is Ransomware
- What is WannaCry ransomware
- Ransomware attacks in India
- What to do to avoid ransomware
- How to remove ransomware
- Ransomware decryption tools – quick heal, trend micro and a few more
- Ransomware extension list
Is Ransomware a Virus or a Malware?
Ransomware is a malicious program which eventually encrypts files on the computer, completely locking you out of your own system.
But the question remains – is ransomware a virus? Not at all. Viruses infect files and programs and replicate themselves. Ransomware, on the other hand, clambers with files and renders them unusable by encrypting them.
How Ransomware Works
Ransomware deploys a number of techniques to gain access to a computer. One of the most effective vectors for deploying ransomware is the phishing spam. Attackers masquerade themselves as genuine enterprises and send emails with malware as the attachment. The email is purportedly disguised to look as much legitimate as it can look.
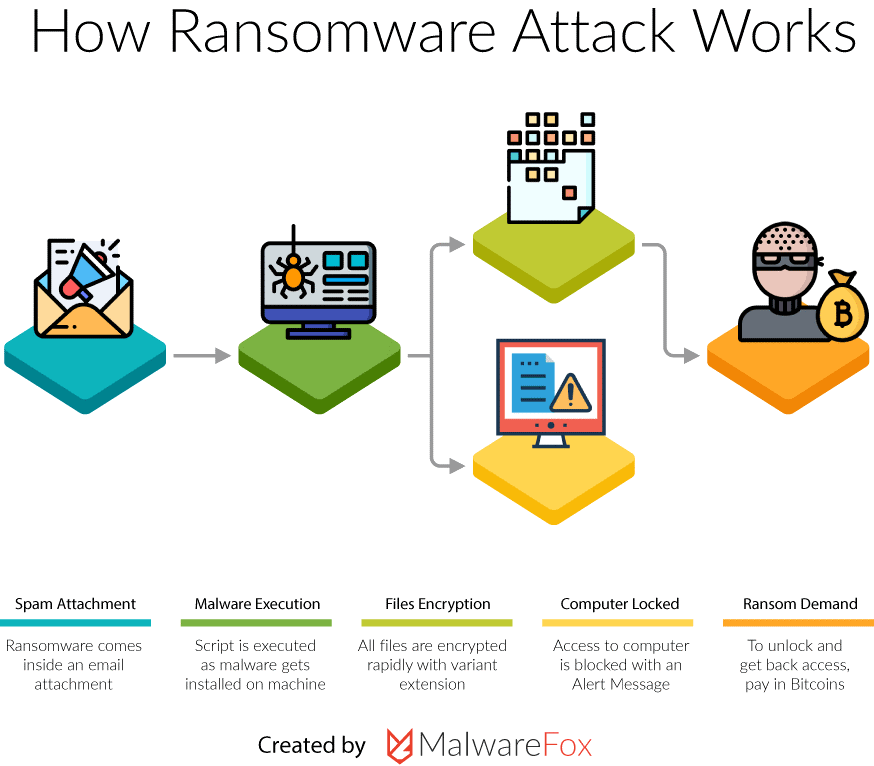
Source – MalwareFox
Once the attachments from these emails have been downloaded and run, the entire system can get compromised. Files, folder – with all their contents – can get encrypted. The ransomware could be in for a treat if there are existing vulnerabilities on your system.
Some highly sophisticated malware have built-in social engineering tools. These malware are so designed that they covertly trick users into allowing them the admin access. Once the ransomware gains access, there is nothing stopping it. Once it gains access to the system, no matter what you do to avoid ransomware, you cannot subdue it.
There are numerous spywares but none comes anywhere close to WannaCry.
Ransom Attacks by WannaCry
Your computer could be vulnerable to WannaCry ransom attacks, without you having a clue of it.
WannaCry is a crypto ransomware. Means, cybercriminals use this spyware to extort money from their victims, which is the intent underlying almost all attacks.
Crypto ransomware is the term used for ransomware that uses encryption to lock files. Note some ransomwares might render files unreadable without actually encrypting them.
WannaCry is the ransom type that locks you out of your computer. A living nightmare for every computer user.
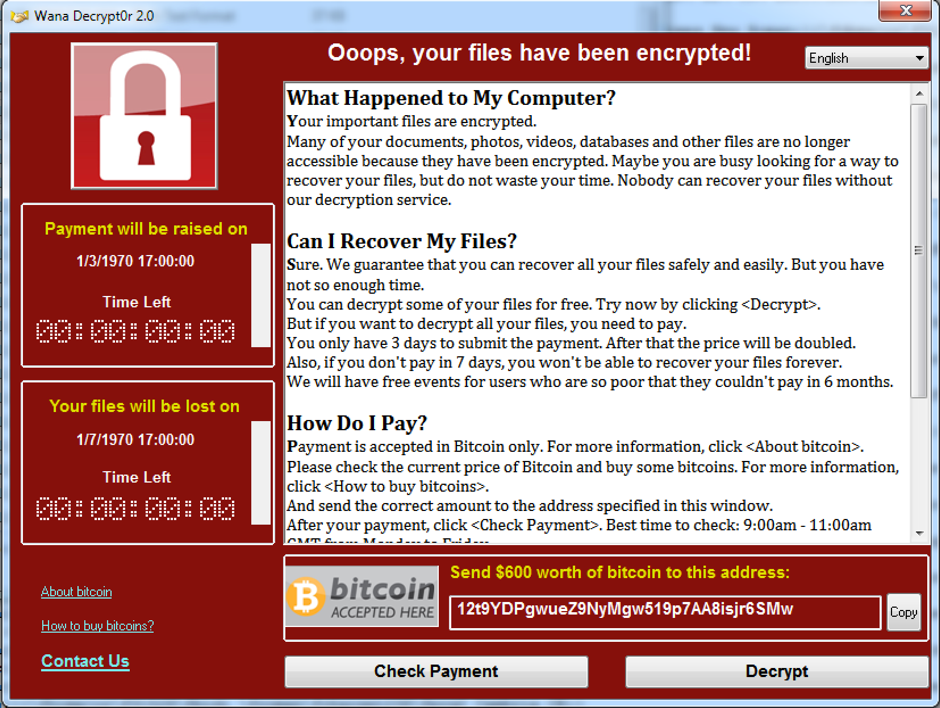
System Attacked by WannaCry Ransomware
WannaCry will take your data as hostage and demand that you pay back to regain access.
WannaCry ransomware allows hackers to only target computers that use Microsoft Windows as the OS. This came after the actors behind this malware were successfully able to dig out vulnerability that the ransomware then exploited.
What was the WannaCry ransomware attack?
The world faced a global pandemic – before the coronavirus – which then came in the form of computer attacks that took place in May 2017.
After the world was struck with the WannaCry pandemic, professionals, individuals and enterprises began searching for remedies. If you have been attacked by WannaCry too, continue reading to learn how to avoid ransomware WannaCry.
WannaCry spread from one Ms. Windows computer to the other, held files as hostages and demanded Bitcoins in return.
Back then most computers only used outdated software, which made the attacks even more lethal. If it were not for the ignorance and lack of awareness among people, the attacks could have been prevented.
What harm can a ransomware do to my computer?
There are several things a ransomware might attempt after it has taken over your computer.
Majority of ransomware are most accustomed to encrypting user’s files. While some may also attempt to send data to a remote server, rendering files remains the priority.
For more technical details on how encryption is done by ransomware, I will link out to a very informative article from medium.
No matter what goes in the background, the end result would be that you are no longer in control of your system and files.
While attempting to access files, the ransomware will present you with a message displaying that all your files are inaccessible.
Guise is the key
The better that the attackers can guise themselves, the more likely are users to trust them.
The easier it is to gain user trust, easier it is to lure users into installing ransomware.

Beware, attachments from anonymous emails could contain malware.
There have been instances where attackers slipped malicious software under the pretext of law enforcement agencies, and later demanded fine.
Attackers have become increasingly artistic and have adopted several variations of extortions.
This is especially true, given that there are ransomware variants called Leakware or Doxware with out-of-the-box capabilities. Doxware works just like any ransomware would except that the ransom is demanded by threating users and publicizing sensitive data.
When under attack, the users are left wondering how to remove the ransomware without a hint of the lethal damage Doxware would be doing.
Finding and extracting such critical information can give attackers a hard time. Further, there are possibilities that the user might not have data sensitive enough to pull off extortion. So, encryption ransomware is, by and large, the most convenient for cybercriminals.
Who is likely to be a target of ransomware?
Studies have shown that attackers carefully choose their targets. These studies also further confirm that hackers prefer attacking organizations, predominantly. This way they are able to inflict maximum damage and thus have a better chance at pay off.
Attackers can choose to target their organization in several different ways. It bows down to where the opportunity lies. Whereas, they sometimes prefer attacking government agencies, hoping to find data that may topple the government or instill national outrage.
Law firms are easy targets and it is here that cyber attackers attain maximum pay outs. Intending to safekeep their privacy – of black deeds – law firms are left with no choice but to settle it off with ransom.
Law firms aren’t very much concerned about exploring ways to avoid ransomware either. They want their clients’ privacy intact and seem not to mind paying meager price for it.
There is no relief here, even if you do not fit any of the categories. There are ransomware that can spread from one computer to another and indiscriminately over the internet.
India, in 2019 became target for world’s three worst ransomware. Ransomware attack in India was led by Ryuk, Purga and Stop.
Ryuk had appeared on corporate landscape a year ago before the alleged attack. Many tout Ryuk as the most creative ransomware ever developed. Ryuk was distributed randomly through backdoor underneath a financial document.
Since the pandemic forced the world to work from home, the industry has rapidly changed. Home networks are a bit less secure than corporate networks, making them more vulnerable. Attacks were sure to increase, especially after telecommuting become the new normal. According to a research by Sophos, “as many as 82% Indian organizations got hit by ransomware in last six months”
The International Picture of Ransomware
Internationally, the so called “advanced” nations aren’t in a better state either. Medical and healthcare sectors are amongst those that are hit the worst.
Brno University Hospital, in the republic of Czech, was the first to take hit. Fresenius, the largest private operator of hospital in Europe, also bowed before a ransomware in May, same year.
Ransomware attacks, however, are not at all exclusive to medical and healthcare establishments. Whether finance or banking, defence or security, every sector has had its share of troubles due to malware.
2020 is perhaps the worst year in the history of mankind, and I say that in every sense. Cyberattacks more than doubled in last 6 months. This has created a sense of urgency in already work-burdened IT cell.
The bitter pill is, India’s internet security tools are way behind their foreign counterparts. So, obviously, the foreign security systems were the first to solve the then mystifying problem: how to remove ransomware.
The ransomware extension list too saw some new entries – probably the greatest addition in a year so far.
Ransomware Extension List
Comodo enterprise has an exhaustive and comprehensive list of ransomware at your disposal. We have listed some of them down below. You can explore more here.
- .Krab Provide
- -email-[email_address].AZER Provide
- .zzzzzzzz Provide
- .f41o1 Provide
- .ppam Provide
- .mdk4y Provide
- .data Provide.GRHAN Provide
- TrumpHead.exe Provide
- .tfude, .pdff, and .tro Provide
What to do to avoid ransomware
Prevention is the method you should ideally be adopting. A penny worth of prevention is a pound worth of cure.
Unluckily, prevention cannot always be successful. This now brings us to the belief people so widely hold that things you cannot prevent are better off detected.
Once you have detected that something has happened to you, you can prevent it from reoccurring on a later date.
-
Never Pay Ransom
Whatever you do, just don’t pay the ransom. Remember, by doing so, you are indirectly funding attackers. It might also encourage them to attack again, now with higher spirits. Even if you pay the ransom, you cannot be sure the attacker will restore access.
-
Never Disclose Credentials
The best bet is to restore impacted files from a backup that you created earlier. Restoring from access points is another way to regain access, and also the fastest.
Do not provide personal information at any cost. Unsolicited phone calls can jeopardize the security of your network, in case you ignorantly disclosed network credentials.
Phishers will try everything they can to trick employees into disclosing their credentials. People asking for information that you deem just too personal should promptly raise an alarm.
-
Antivirus & Firewall
Antivirus and firewall can help safeguard network security. A strong firewall configured with updated applications helps keep attackers at bay. It is important that you use a reputed antivirus. The last thing you would want is to buy a cheap antivirus and ending up getting sold a malware instead.
You should routinely scan content and filter your email. Care must be taken while downloading attachments.
Make sure all the software and applications are up-to-date with required patches.
-
Deploy VPN
When on a public network, use trusted Virtual Private Network (VPN). Alert your IT department when on a business trip.
As organizations defending threat networks become more and more powerful, cyber attackers are prying on novel vulnerabilities. Malware has become powerful like never before. Attackers are now deploying a number of evasive techniques that not only avoid detection, but are also ten times more lethal.
In past few weeks, ransomware has been passed into victims under the pretext of fake COVID emails. Some advance level ransomware communicate via the dark web, to avoid IP backtracking. The connections over dark web are anonymous and retracing communication end points is not possible at all.
Ransomware Can Spread Very Quickly – The Main Problem
By the time you figure out ways to avoid ransomware, it would have done enough damage for a lifetime.
When it comes down to who is more likely to get attacked, it all bows down to the same – we are all at the same level and have equal chances of being victims.
Maersk, one of the largest logistics to exist, may have the perfect story to narrate. Until now, we had not through that ransomware could be so contagious. Turns out, it is. Maersk, in 2017, became victim of ransomware NotPetya. The malware was able to inflict damage on as many as 50,000 endpoints, and equal number of servers in more than 120 countries.
How to decrypt files encrypted by ransomware
For a moment of relief there are tools that can decrypt files encoded by the ransomware but the program may or may not always succeed. Still, a decryption tool is worth the try.
- Before you use the decryption tool, make sure you have an antivirus that has removed the infection from your computer. If the infection still exists, remove it. Else, watch the malware encrypt your decryption tool. Do some research on “how to remove ransomware” before you proceed.
- No tool can assure you 100% decryption success rate. Different tools are effective against different threats. So, before you begin, identify the ransomware. Having identified what attacked you, you can move on to download the tool designed specifically to tackle that malware.
To identify malware – note the extension name of the files that it has encrypted. The warning message relayed by the malware sometimes also states its type.
- Each decryption tool is different, both in terms of interface and functionality. Read user guide to know how to once before proceeding with decryption.
If all went well, your computer – with all its files – should be up and running in a few minutes.
Ransomware decrypt tools that are worth the try
-
Rakhni Decryptor
Designed by Kaspersky, Rakhni Decryptor is the most renowned of decrypt tools. It has been named after it success in decrypting ransomware Rakhni. It is also touted as effective for ransomware like –
Agent.iih, Dharma, Aura, Version 2 & 3 of Crysis, Rotor, Lamer, and a few more including TeslaCrypt.
-
WanaKiwi
WanaKiwi is perhaps the single most effective antidote to WannaCry. WanaKiwi provides an easy way to decrypt and recover files that have been encrypted by WannaCry.
The decryptor is supported on almost all Windows versions.
Note – WanaKiwi can only recover files if Wannacry has not been killed i.e. the system should not be rebooted even once after the attack took place. WanaKiwi cannot recover files on a rebooted PC.
-
Trend micro ransomware file decryptor
The trend micro ransomware file decryption tool gets most frequent updates. Trend micro has now also included newer updates, making it capable of decrypting files encrypted by CERBER family of ransomware (CERBER majorly targets Office 365 users).
Trend micro is known to work on almost a dozen families of ransomware. This includes –
- SNSLocker
- AutoLocky
- BadBlock
- CryptXXX V1, V2, V3*
- TeslaCrypt V1, V2, V3, V4**
- SNSLocker
- 777
- XORIST
- TeslaCrypt V2**
- XORBAT
- And the most recent CERBER
Ransomware is profitable for its creators and very devastating for the users. Thankfully, many researchers and security firms have created free decryption tools to decrypt the files or data encrypted by ransomware. If you are affected by ransomware, here are some free ransomware decryption tools that can help you get your data back.
-
Quick heal ransomware decrypt tool
Quick heal’s ransomware decryption tool is known to work on most ransomware. Quick heal was among the first to detect CryptoLocker, that demands a ransom of $ 300. The tool is available for free and is known to target most malware well.
Source – Quick Heal
Takeaway –
We hope you now have an in-depth understanding of Ransomware, including its detection and decryption using decrypt tools. To remind you again, a penny worth of prevention is a pound worth of cure. While there are numerous way to remove ransomware, not all may work. The best you can do against malware is to prevent it from entering your system.






 Live Chat
Live Chat
This post offers clear idea designed for the new people of blogging, that genuinely how to do blogging and site-building.