Table of Content
Virtualization isn’t for nerds alone or people running powerful supercomputers and servers. VM (and virtualization) has something to offer to everybody. If you have been thinking whether VM would be any useful, it is about time you tried it yourself.
So here we are, with some Virtual Machine project ideas. You can try these out for your school or college level projects while still being able to have fun with it.
What is Virtualization?
Virtualization, per se, is the act of running several operating systems in one physical machine. Each OS in a virtualization environment is so configured that it behaves as if the other operating systems never existed.
Virtualization is achievable in your desktop too. Several applications such as VMware are available for download. (We highly recommend that you install this application and dabble with the things that we have mentioned below.)

Source – VMblog
There are two ways in which the operating systems co-exist in virtualization –
- The OS’s could run parallel to one another. In such scenarios, the operating systems are managed by a program called the hypervisor. Hypervisor oversees operations of all OS’s in a physical machine. The OS’s may or may not be aware of each other’s existence.
- Multiple operating systems can also exist one within the other i.e. one OS will run another OS. This, usually, is done within the program window. Means, a separate application will help you to navigate through the guest OS from the host.
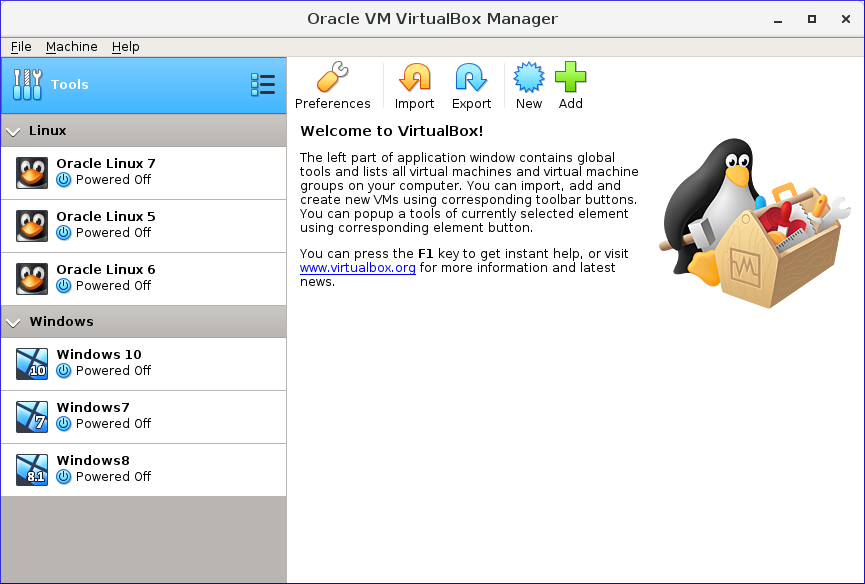
The latter is also called OS-level virtualization and is the most prominent in laptop and desktop computers. Several applications such as VMware and VirtualBox (an Oracle product) are leading in the domain.
What is a virtual machine?
If virtualization is the process, VM is the end-product. In layman’s terms, virtual machines are virtual, software-based environments that act as physical machines even though they are not.
The logic is simple, virtualization is implemented in VM. That is to say, when you implement virtualization, you are said to be operating a VM.
Virtualization and virtual machines are often confused and used interchangeably. The former is the process while the latter is its product.
What does VM do?
Virtual machines mimic hardware capabilities to run applications that could not be operated efficiently on the host OS. The benefits of virtual machines lie in the fact that it helps developers to emulate applications that the host would not otherwise support.
The Guest and the host
As we have been emphasizing, a single machine could have multiple operating systems, the OS’s co-existing in parallel or one inside the other.
The concept of host and guest arises when VMs are run within an OS. The primary operating system of the computer comprises the host, whereas VMs that are configured inside the host are known as guests.
Having tuned ourselves to the basics of virtualization, we now take a look at 7 things you probably did not know you could do with VM.
Here are the 10 things you can do with virtualization that might convince you that it’s worth trying, if you haven’t tried already.
- Run discontinued Apps
There are some really cool apps and games that no longer work on Windows 10 but worked seamlessly on Windows XP. I have had this issue too. Since Windows XP has been discontinued too, I am not enough compelled to delete my existing Windows 10 and roll back to XP.
If you have had similar concerns, you should try running a VM. You can easily install XP on a Windows 10 computer while on a VM. XP will offer you an immersive experience of the same taskbar and you’d be able to run your game flawlessly.
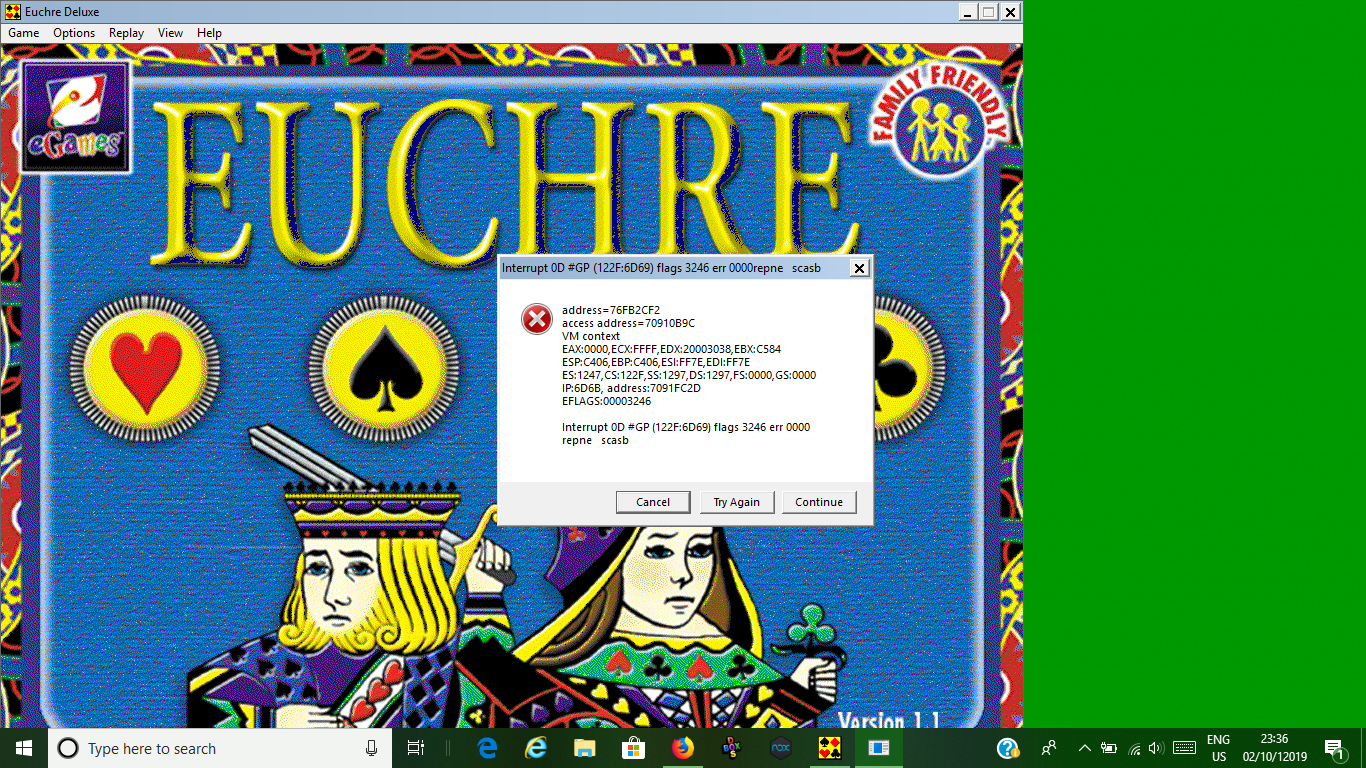
VMware features Unity mode. With Unity mode, you can maximize your guest OS all over the screen to make it seem like host OS. Not for a moment, you would know that the window is not a real machine but a virtual operating system running as “guest”.
You can run older programs too, just install a program called Virtual Box and start running discontinued apps on free Virtual Machines.
- Disaster Recovery
Disaster recovery is the number one reason why developers use VMs for development assignments.
I, personally, believe that disaster recovery with VM is more enticing to enterprises than it is to individuals chilling at home.
Disaster management and recovery remain the top priority for enterprises around the world. Despite a plethora of backup services, VMs remain the preferred solution.
Recovery hasn’t been easier than it is with virtual machines. VMs with all its isolated resource helps safekeep the data in a remote environment. This might not be the case with OS-level VMs though, but it is crucial in workstations and servers.
Files on one VM never impact files or inhibit activities on other virtual machines. Similarly, if files on one of the VMs gets deleted, data on the adjoining VM remains intact. This is the methodology behind disaster recovery that makes it crucial for organizations.
- Access Data infected with Virus
I once received a file that was important for my work but the antivirus somehow flagged it as harmful. I had no choice but to open the file, but I was also concerned about the security of my computer.
Luckily, I had a virtual machine in the place and that simplified a number of things for me. There are malware that have the capability to break into VMs, but not all malware are as advanced.
Most virtualization applications include the snapshot functionality which means you can create a small private disk space of the virtual machine.
With the snapshot created, you can open infected files without putting the entire system in jeopardy. It is like having your own island. Things that take place on the island does not affect the outside world.
- Migrating and backing data from legacy Systems
Legacy systems aren’t ordinary systems. They are more than a bunch of outdated applications and contain files that might be useful in the future.
With the advancement in time, legacy systems become inefficient and cumbersome. Modernizing IT infrastructure is essential because the outdated system, at one point, starts to cost you more money.
The longer you allow these outdated systems, the more likely you are to lose productivity. But the data created on these systems aren’t any less important than they were once.
With VMs, you can easily migrate files from older systems. If you made hardware changes, you would still be able to run older programs on a VM and users won’t know if anything changed at all.
- Incognito with Virtual Machines
Despite numerous advantages of a virtual machine for web browsing, we have not given VMs their due credit.
Let’s face it, incognito mode on a browser does not store history, cache and cookies, but people would still be able to discover you.
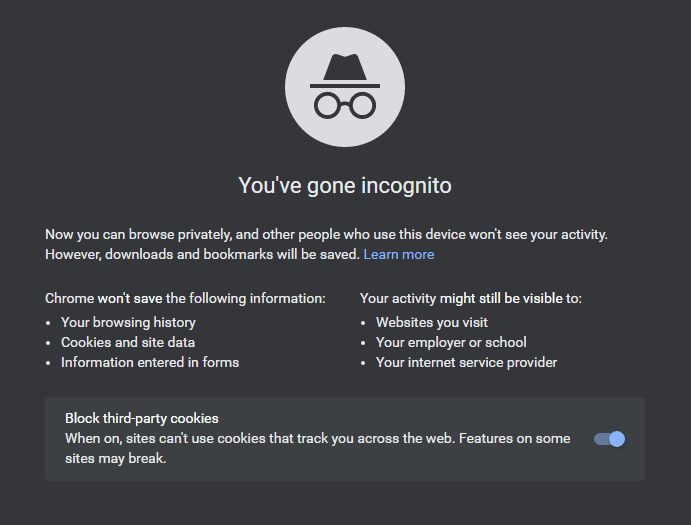
Incognito only hides you from yourself and you are nearly as much discoverable as you were without incognito.
For those who are hyped about privacy, VMs can offer next-level discretion by spoofing you as someone else. You can have two independent systems –
- First, your original host for all the things you do.
- Second – the VM – running a virtual private network, for private browsing.
While your ISP provider and the web client would still see what you are up to, they wouldn’t know who you are truly.
- Test upgrades
I do not see a reason why you wouldn’t use a VM to test whether software updates are stable or buggy. You shouldn’t jeopardize the security of your original host by configuring an upgrade full of bugs.
You could play smartly and test new applications, updates and software on your VM before rolling them out on your primary OS.
Server admins use virtualization to duplicate an existing OS installation which they then use to test operating systems. Server administrators use this copy of the OS to check whether changing configurations would cause any harm to the system.
When everything seems to work normally, the changes are rolled out to the primary installation of the OS.
- Run Windows over Linux or Mac (or vice-versa)
Of all the fun things to do with a VM, nothing is as intriguing as running Windows over Mac – or one OS over the other. Mac users have been running Windows and Linux as VMs because the same OS could appear as boring when used for long.
As long as you are able to install a distro on your VM, you could do just about anything on your guest OS.
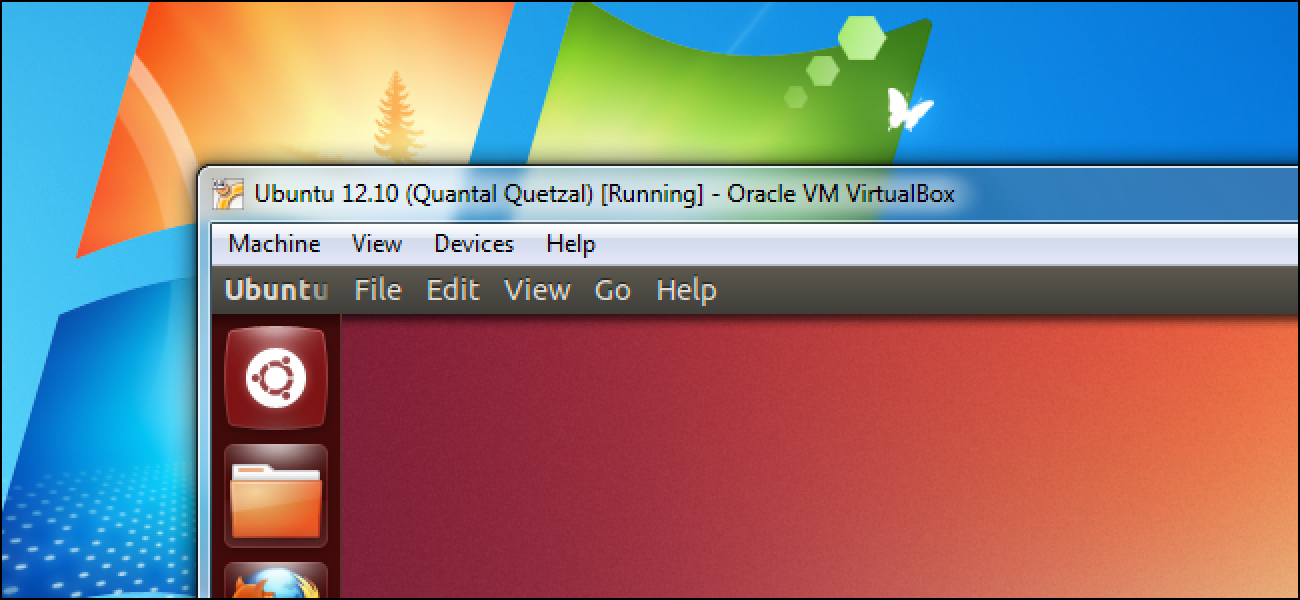
Users that have been running Linux servers can run Windows for the feel of its GUI. Windows users can install Linux and know what it means to not have root-access denied on their computer.
This way you would be able to combine the best of two technologies and operating systems.
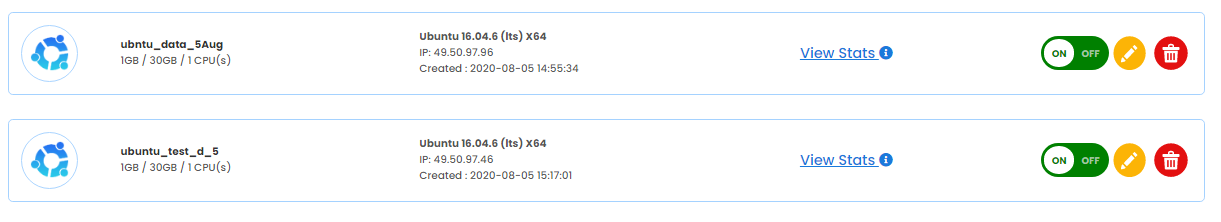
- Create your own Cloud Computer
We know it, you cannot carry your laptop everywhere, but you cannot compromise work either.
If you are out of your office premises, you either need a laptop (and access to your network) or a VM on cloud servers.
Mobile phones work fine for remote working. You can leave your laptop running and carry your mobile with you. Configure remote desktop connection using your mobile. This would allow you to access the desktop environment but on a different screen.

The other way out is to deploy VMs on the cloud and access it from mobile. Yes, it is possible, although the interface would be devoid of fancy graphics, it is still workable.
You can setup your system to accept Remote Connection Requests automatically. This way you would be able to easily access the remote computer when the connection breaks.
Do note the public IP address of the router your system is connected to. This way you can configure port forwarding of the RDP requests made on your laptop.
- Internet Sandbox
Ultimately, the coolest way to use VM is to isolate it from the network. Sounds daunting right? Here is the trick.
Your computer is discoverable in a network. The administrator might have an eye upon the things you do. The best way to evade malicious eyes is by setting up a VM.
By configuring a virtual machine, you can technically create a computer within a computer. While you continue to work on your host, the VM will show as a separate user in the list of connected devices.
You can continue working the way you usually do on your computer and reserve the VM to disguise yourself under the false identity. People will malicious intent, spying on your computer, would never know who the person behind the VM is and what is he up to.
This is called internet sandbox. In short, the sandbox is the space you create to isolate software installations from the original OS.
- Reuse Old Hardware
In point 4 we discussed how legacy systems can be upgraded without changing the overall user experience on the system.
As systems become old, they are not completely discarded but brought to use in less important tasks.
Though not as powerful, outdated systems are still useful for light-weight applications that need little computing powers.
You can combine the older, less powerful computers with your current workstations and augment resources by combining the two. This way, you would be able to delay the upgrade and save on upgradation expenses.
Though the above process is manually done, you can install Citrix XenDesktop on your server to automate resource allocation.
XenDesktop is a really powerful utility that I have been using for a long time. It allows remote desktop facility too but the server should be tweaked to allow public access.
Remote connections can be made using mobile phones and tablets.
With Citrix, you can smartly configure client’s desktop space and provide the same level of user experience. When the client chooses to run animation and videos, you can smoothly shift processing to the client computer. The difference would be little noticeable.
Upshot

Do you want to deploy virtual machines on remote servers? Enjoy the best performance, scalability and accessibility possible on a VM with Go4hosting’s cloud servers. Revitalize your business with the robust and austere architecture of Go4hosting’s cloud server hosting and enhance productivity like never before.






 Live Chat
Live Chat